Many of us enjoy gaming and it makes the experience that much more fun when you can enjoy it with friends online. However, have you ever stopped to wonder and ask yourself, how safe online gaming is?
Online gaming
Technological developments especially the advent of personal computers in the 1970s greatly accelerated the growth of online gaming. Furthermore, the creation of high-speed (broadband) internet connections has stimulated the evolution of new gaming genres such as the massively popular multiplayer online role-playing games (MMPORGs). Currently, some of the most popular online games are Dota 2 (one of my personal favourites), War Thunder, League of Legends, Planet Side 2, Lineage, and Star Wars: Old Republic.It is estimated that half a billion people play online games on a daily basis. Most games can now be played on PCs, consoles, and mobile devices. According to a US based study, more than 40 percent of online time is spent on 3 activities - social networking (22.7%), gaming (10.2%) and emails (8.3%).
Online gaming has become a huge and lucrative industry. A recent global games market report showed that the global games industry reached revenues of USD99.6 billion in 2016 and could exceed USD102.9 billion in 2017. The popularity of online gambling has also increased and already had an estimated 937 million gamers in 2012. You can now play most of your favorite games such as poker,blackjack, baccarat, and roulette live, interacting with live dealers and fellow players. The thrill and excitement of winning is all the more exhilarating if you play for real world money. People can also play slots in a secure online casino, lotteries, bingo, as well as place sports bets. Industry analysts predict that revenues derived from the global gambling market will reach USD 1,009 billion by 2020. Unfortunately, because online gaming is such a profitable industry, it is also set to become the next big target of cyber crime.
The Dangers
The results of a 2016 crime survey conducted in the UK revealed that 6 million online offences had been committed, and one in ten persons in that country had been victims of various cyber crimes. The report warned that people are “more likely now to be mugged online than in the street.” The most shocking statistics for me is that most of the time you have no idea that you’ve become a victim until it’s too late.Some of the most common cyber crimes and risks associated with online gaming involve identity theft, fraud, phishing, stealing your banking and credit card information, counterfeiting, privacy violations, software piracy, hacking of email and social media profiles, computer virus attacks, cyber bullying, and kidnapping. Online shopping scams and those involving dating sites are some of the other cyber crimes to be on the lookout for. Crimes involving children are also increasing as they are more exposed and naïve when it comes to the dangers of playing online multiplayer games such as Minecraft.
Protecting yourself
So how can you protect yourself when gaming online? How well are you protecting your information from being stolen, used and sold? Some tips are just common sense and being alert and awareTo avoid some of the common risks associated with online gaming make sure that you incorporate the following tips to improve your online security.
- Start by just using plain old common sense. E.g. If a deal is too good to be true it usually is.
- Be alert, and be cognisant to the fact that the threat is real
- Internet security software
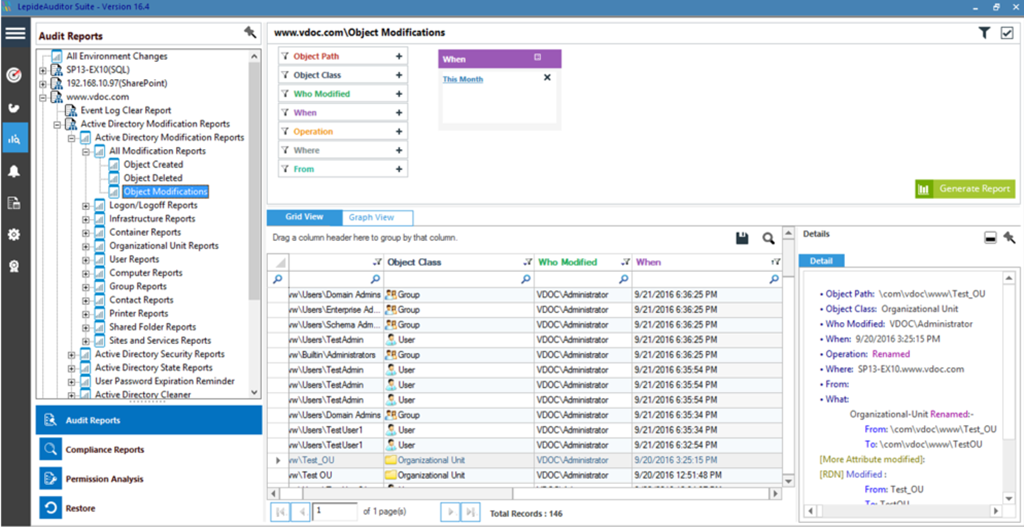
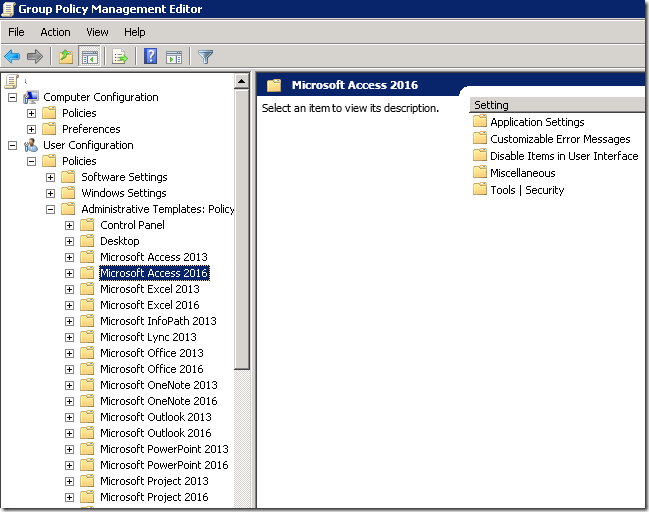
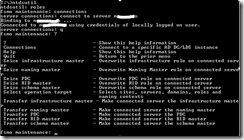
- Ensure that you have installed up to date internet security software. This should include secure firewalls, antivirus and antispyware programs. Also secure all remote connections. Some good free software are AVG, Avast, and Malwarebytes.
- Passwords
- There are so many online activities that require a password - online banking, a multitude of social media platforms, forums, gaming, e-mail and tons more. Remember all websites don’t practice the same level of security. That is why you should NOT use the same password for the simple reason that if you have been compromised,they would have only gained access to that one platform.
- Consider using a password manager to encrypt your passwords. Always use strong passwords. I personally prefer to use long phrases e.g SummerIsGre@t , IL0veDota2, SeeingIsntAlwaysBelieving , WhoTheMan? , BigBoysDontCry . These are example of password that are long but easy to remember.
- Personal Information
- NEVER disclose any of your personal information to other players. Also be careful not to reveal your personal information in your username, or where possible when creating a personal profile. Ensure that you delete all personal information should you sell your game consoles (mobile or pcs).
- Avoid Ad supported games
- These games still need to make money and usually do so by selling your information to other websites that often result in unsolicited mail.
- Use reputable gaming platforms
- Steam – a wide range of both free and paid games that practice good security such as two factor authentication, email verification, SSL
- Casino.com if you prefer playing games to win real world cash. – Reputable, SSL and fully licensed
- Clash of Clans – for mobile gamers on IOS and Android
- Choose platforms that offer good email and telephonic support
- Children
- If you are a parent, ensure that you set clear rules and guidelines for your children when they are playing online. It may be best for younger children not to be allowed to play online games with strangers.
Online gaming is a dynamic and ever changing industry. Today’s gaming genres have come a long way since the early days of Atari consoles and Arcade gaming that was so popular in the 1980s. Gaming has also become firmly embedded in modern popular culture. So where to from here? Virtual reality games and games using artificial intelligence technology are currently being developed. These are new and exciting developments that will keep millions of gamers enthralled. It’s clear that gaming is and will remain a wonderful form of entertainment to connect with friends and family. However, safety should always remain a serious consideration when you are online whether you are gaming, banking, shopping, or connecting with friends on social media.
Have you been a victim due to lack of security on any online gaming platform? Do you use two factor authentication? Are there any additional security precautions you take when playing online, not mentioned here? Let me know in the comments below.





















![image_thumb[23] image_thumb[23]](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEgXX9DjTmKkM8ssi6QKt2aeyk-AutvSPQfhe_yWtbROo5XTEI_FfPOQx8ADqTGp1tI7PVKIHs4Iz9S-V6qaLRetdcUEN0T_YbP4k-n65YPGJHQ13ep4S3JzJe3mrTkpQ95a3RMegHCqKuY/?imgmax=800)
![image_thumb[22] image_thumb[22]](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEhY7qrLpWuETtoEA2pnJNOMpTn8jzNcEwE0i9Y5Oh47a1BuuwswsBUW7oWXluxiIuw4LSeZJ0IZnuZug2DHQXpj3m9EMraZOwKw1LuOOWuFlFw8a53QcKzlFKp60rvpv7rh37v2ug3lDr8/?imgmax=800)
![image_thumb[21] image_thumb[21]](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEjMhYc6-GcurQ33kiOGMM67TQzpluRxMnAPZWrBp1GOMJ2ASQ4b0VUtPWtJWlusAMV-l-b7Q0c5lk7YRLJeyAGD53EZQTdo-qbkCUhV0x6zFe8FmMkxqirF63TC2zfvTGC8ua7qSvu45jY/?imgmax=800)
![image_thumb[20] image_thumb[20]](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEia6Igb_d4I1tIGGyMzzkksuZ8upjvQiZE76d_TPTeapE-TJpGWkxSNqE34-Qmm6OptsK1bmZXVSFYHtZ1G5zIUsKFvaPllj2C28aSSdsgJspNGEogpnccnWwq8dKKXIb-PvufabU_xaDo/?imgmax=800)






















 Popular
Popular
 Tags
Tags
 Videos
Videos



